Edge computing data governance failures are rarely discussed, yet they explain why many edge projects fail despite strong technical foundations. On paper, it looks solid. In practice, many edge computing projects fail quietly. Not because of hardware limitations or network speed, but because of poor data governance.
Most teams underestimate how messy data becomes once it leaves the centralized cloud. These patterns explain why edge computing data governance failures repeat across industries.
The Real Problem Isn’t the Edge — It’s the Data
Edge computing shifts data processing closer to where data is generated. Sensors, cameras, and local devices suddenly make decisions on their own. That sounds efficient, but it introduces a basic question many teams can’t answer:
Who owns the data at the edge?
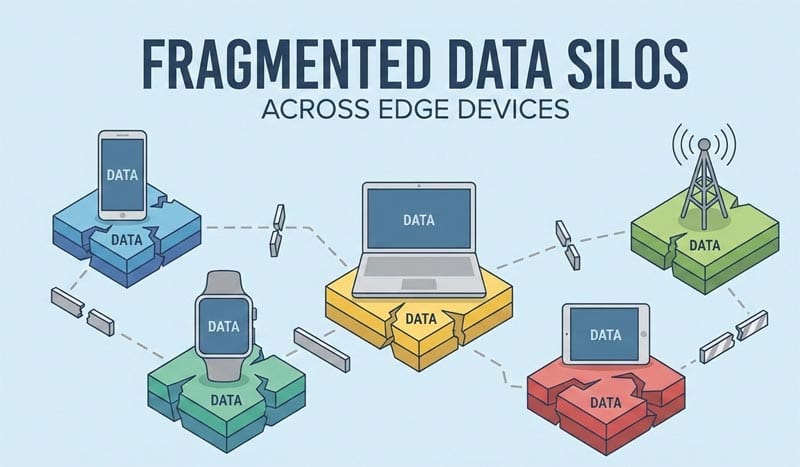
Without clear data ownership rules, edge systems turn into fragmented silos. Different devices collect data in different formats, follow different retention rules, and apply inconsistent security policies. Over time, the system becomes unmanageable.
This is where edge computing data governance failures usually begin.
Why Traditional Governance Models Break Down
Most data governance frameworks were designed for centralized systems. They assume:
- One primary data store
- Clear access controls
- Centralized compliance monitoring
Edge environments break all three assumptions.
Data is created, processed, and sometimes deleted locally. There may be hundreds or thousands of edge nodes. Applying cloud-era governance rules directly to edge computing simply doesn’t scale.
As a result, teams rely on shortcuts. Logs are incomplete. Data lineage is unclear. Compliance checks become manual or are skipped entirely. These shortcuts accumulate risk.
Compliance Becomes a Silent Liability
Regulations like GDPR and sector-specific data rules don’t care where data is processed. If personal or sensitive data touches an edge device, governance still applies.
Many edge projects fail audits not because data was misused, but because teams can’t prove how data moved through the system. No audit trail means no compliance defense.
This is one of the most common edge computing data governance failures, and it often surfaces only after deployment.
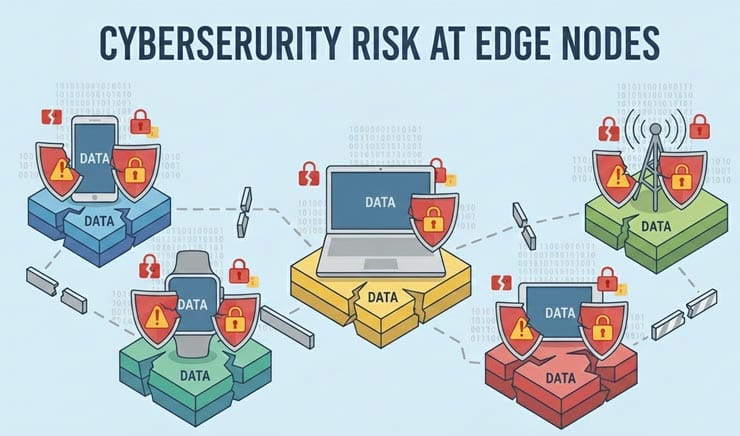
Security Gaps Multiply at the Edge
Every unmanaged edge node is a potential attack surface. Without governance policies that define:
- Data classification
- Encryption standards
- Access expiration
Security becomes reactive instead of systemic.
Edge security tools alone are not enough. Governance defines what must be protected and why. Without it, security teams are guessing.
How Successful Teams Avoid These Failures
Teams that succeed with edge computing treat data governance as infrastructure, not documentation.
They:
- Define data ownership before deployment
- Standardize data schemas across edge devices
- Automate retention and deletion policies
- Enforce governance rules at the device level
This approach doesn’t slow down innovation. It prevents edge systems from collapsing under their own complexity.
Final Thoughts
Edge computing doesn’t fail because the technology is immature. It fails because data governance is treated as an afterthought.
If governance isn’t designed for the edge from day one, scale becomes a liability instead of an advantage. And once edge systems sprawl, fixing governance retroactively is expensive and disruptive.
In edge computing, speed without structure is not progress.
Without addressing these foundations, edge computing data governance failures become inevitable at scale.
Why Data Governance Is Often Ignored in Edge Projects
Many edge initiatives start as technical experiments rather than long-term systems. Teams focus on deployment speed, hardware efficiency, and latency benchmarks. Data governance is seen as something that can be “handled later.”
The problem is that edge environments scale faster than governance models can catch up. Once devices are deployed in the field, enforcing consistent data rules becomes significantly harder. This delay creates invisible risk that only surfaces during audits, incidents, or system expansion.















