Our digital lives are amazing, aren’t they? From smart homes to online banking, almost everything we do touches the internet. But with all that convenience comes a flip side: digital threats. It feels like every other day there’s a new story about a data breach or a clever scam. The bad guys are always evolving, which means our defenses have to evolve too. We can’t keep fighting tomorrow’s battles with yesterday’s tools. That’s why folks in the know are already building what we call future cyber defense – a far more advanced, intelligent, and proactive digital shield designed to protect our increasingly connected world. It’s about moving beyond simply reacting to attacks, and instead anticipating and even preventing them.
TL;DR
- Advanced cyber defense uses cutting-edge tech to stay ahead of evolving online threats.
- AI-driven security is key, helping to predict attacks and automate responses.
- Proactive protection focuses on identifying vulnerabilities before they’re exploited.
- Zero-Trust architecture means verifying every user and device, every time.
- Your personal digital resilience is crucial – you’re a vital part of the defense.
- The goal is to build a smarter, more adaptive digital environment for everyone.

Consider this: our devices are getting smarter, our networks are getting faster, and our data is growing exponentially. This creates more potential entry points for those looking to cause harm. Simple antivirus software and basic firewalls, while still important, just aren’t enough to handle the sophisticated attacks we see today and will see tomorrow. We need a fundamental shift in how we approach digital safety. We’re moving from a reactive stance – patching up vulnerabilities after they’ve been found – to a predictive and even pre-emptive one.
AI-Driven Security: Smarter Than Ever
One major shifts in future cyber defense is the rise of AI-driven security. This isn’t science fiction anymore; it’s happening right now. Imagine a security system that doesn’t just check a list of known bad guys, but actually learns what ‘normal’ looks like on your network or devices. When something deviates from that norm – even slightly – it flags it instantly. AI can process vast amounts of data much faster than any human team, spotting patterns and anomalies that would otherwise go unnoticed.
This means attacks can be detected and often neutralized in seconds, not hours or days. It’s like having a hyper-vigilant guard dog that not only barks at strangers but can tell the difference between a delivery person and someone trying to break in, even before they reach the door. This capability is vital for combating polymorphic malware, which constantly changes its code to evade detection, or sophisticated phishing campaigns that mimic legitimate communications almost perfectly.
- Pro-Tip: Understand that AI tools are getting better at identifying very subtle signs of compromise, making traditional ‘signature-based’ detection less reliable on its own.
- Common Pitfall: Don’t assume AI security is a ‘set it and forget it’ solution. It still requires expert oversight and continuous training to adapt to new threats.
Proactive Cyber Protection: Stopping Threats Before They Start
Beyond simply reacting faster, the next generation of defense is all about being proactive. This involves several layers of strategy aimed at stopping threats before they can even make contact. One key area is ‘threat intelligence.’ This isn’t just about knowing what’s out there today, but analyzing global attack trends, understanding hacker motivations, and predicting where the next wave of attacks might come from. Sharing this intelligence among organizations and security researchers allows everyone to be better prepared.
Another crucial element is ‘Zero-Trust architecture’. The old way of thinking was, ‘Once you’re inside the network, you’re trusted.’ Zero-Trust flips that on its head. It says, ‘Never trust, always verify.’ Every single user, every device, and every application trying to access resources – whether they’re inside or outside the traditional network perimeter – must be authenticated and authorized. This drastically reduces the damage if an attacker somehow gains a foothold, as they can’t move freely through the system.
- Pro-Tip: Look for security solutions that integrate global threat intelligence, as this collective knowledge significantly strengthens your defenses against emerging threats.
- Common Pitfall: Thinking ‘Zero-Trust’ means everyone gets blocked. It’s about granular access control, ensuring people only access what they absolutely need, when they need it.
Your Role: Building Personal Digital Resilience
While big tech companies and governments are building these advanced digital shields, you, as an everyday user, play a huge part in personal digital resilience. After all, the most sophisticated system can be undermined by a simple human error. Understanding the basics, and applying them diligently, forms a critical layer of our collective future cyber defense. This includes things like using strong, unique passwords for every account, enabling multi-factor authentication (MFA) everywhere it’s offered, and being wary of suspicious emails or texts.
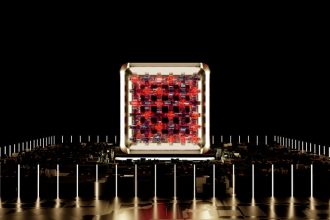
It also means staying informed. Knowing what a phishing attack looks like, understanding why software updates are important, and recognizing the signs of an infected device are all parts of being resilient. All these sophisticated systems, from AI spotting anomalies to automated responses, rely on incredible processing power. The very chips that make our devices smart also enable these defenses. Keeping up with this pace requires constant innovation in underlying hardware. To learn more about these powerful components, check out how next-gen chips are shaping our world and fueling these advancements.
Real-World Impact: What This Means for You
So, how does all this advanced cyber defense actually affect your daily life? The goal is a smoother, safer digital experience, even if you never directly interact with the AI or Zero-Trust systems. Here’s a glimpse:
- Safer Online Banking: Banks are using AI to detect fraudulent transactions faster, often before you even realize something is wrong, protecting your money.
- Protected Personal Data: From your healthcare records to your shopping habits, advanced systems work behind the scenes to keep your sensitive information locked down and private.
- More Secure Smart Homes: As more devices connect to your home network, proactive defense helps shield your smart fridge, security cameras, and voice assistants from being exploited by attackers.
- Less Spam and Phishing: While never entirely gone, AI-driven filters are constantly improving, reducing the amount of junk and dangerous emails that reach your inbox.
- Business Continuity: Companies that are well-defended are less likely to suffer breaches that could interrupt services you rely on, from online streaming to utility providers.
Common Misconceptions
- My old antivirus program is all I need to be safe.
- I’m too small or unimportant for hackers to target me.
- Advanced cybersecurity is only for massive corporations with huge budgets.
- It’s impossible to truly be secure online, so why bother trying?
- Cyber defense is purely about technology, not about people or policies.
Next Steps
Ready to strengthen your own digital shield? Here are some immediate actions you can take:
- Enable MFA: Turn on multi-factor authentication for every account that offers it – email, social media, banking, shopping. This is the single most effective step you can take.
- Update Everything: Make sure your operating system, web browser, apps, and antivirus software are always updated. These updates often contain critical security fixes.
- Use a Password Manager: Create strong, unique passwords for all your accounts without having to remember them yourself. A password manager does the heavy lifting securely.
- Be Skeptical: Before clicking a link or opening an attachment, pause. Does the email or message seem legitimate? Does it come from a familiar sender? If in doubt, don’t click.
- Back Up Your Data: Regularly back up important files to an external drive or cloud service. If you ever fall victim to ransomware or a data loss event, you’ll be able to recover.
- Stay Informed: Follow reputable tech and security blogs (like this one!) to keep up-to-date on the latest threats and best practices. Knowledge is a powerful defense.